Executive Summary
Threat actors use every method to achieve their motives. The motives vary from financial, espionage, destruction, etc. The Police Trojan website is a classic example of a website impersonating the National Crime Records Bureau with a fake message “Your browser has been locked” and using scareware techniques to make users pay for accessing pornographic content.
Scareware: Malware/websites use social engineering techniques to cause shock, anxiety, or the perception of a threat to manipulate users into downloading software or making a payment.
Shreshta Threat Intelligence has recently detected a phishing website that impersonates the National Crime Records Bureau (NCRB) with a fake message informing that the user’s computer has been locked and that the user has to pay a fine for accessing pornographic content.
About National Crime Records Bureau
The National Crime Records Bureau (NCRB) is an Indian government agency responsible for collecting and analyzing, crime data as defined by the Indian Penal Code (IPC) and Special and Local Laws (SLL). NCRB is headquartered in New Delhi and is part of the Ministry of Home Affairs (MHA), Government of India.1
Motive
The fake website uses social engineering tactics to scare users by generating fear in their minds. The message on the website “Your Browser has been blocked due to repeated visits to pornographic sites containing materials prohibited by the laws of the India, namely, pornography promoting pedophilia, violence and homosexuality.”
The motive of the threat actors is to harvest users’ credit card information.
Technical analysis
Your browser has been locked
Figure 1 – Upon accessing the phishing website, the user is presented with a prompt instructing them to reload the page.
Upon clicking either of the buttons, the user is redirected to the following page which then enters into full-screen mode. This gives the impression to the user that their computer has been locked.
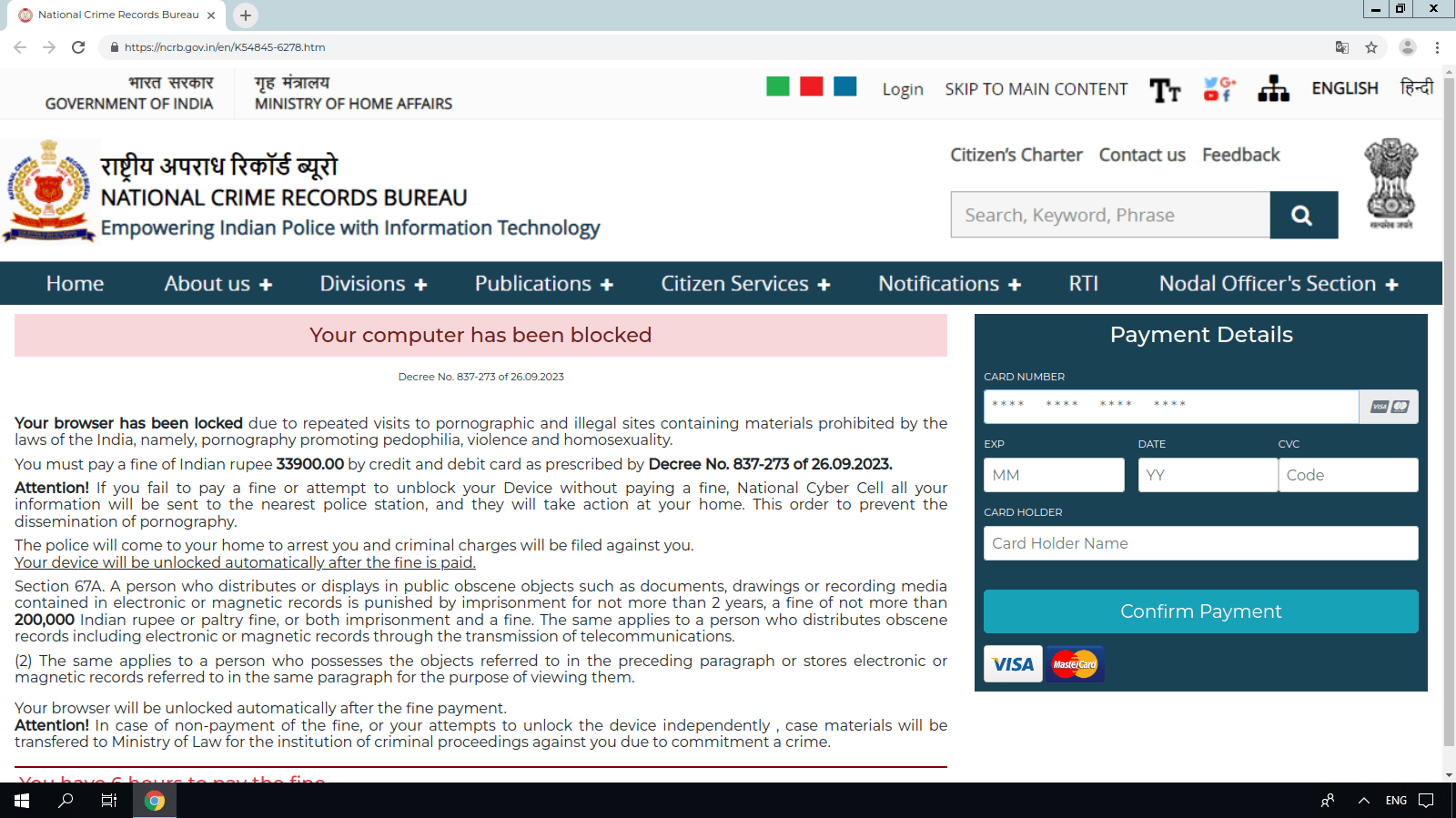
Figure 2 – The phishing website uses social engineering techniques to scare the user and prompts the user to enter their credit card details
Flow of the attack
- The user gets redirected to the fake website
- The user clicks on “Reload” or “Cancel.”
- The website redirects and loads in full-screen mode a fake page impersonating the National Crime Records Bureau.
- Clicking anywhere on the page doesn’t work except for the input under Payment Details. This gives the false impression to the user that their computer is locked.
- The only option to exit the full-screen mode is to press the “ESC” key, which returns the user to the main browser window.
Safety Recommendations
- A message received by email/SMS/Whatsapp with a tone of urgency should be dealt with with extreme caution.
- Scareware websites are generally associated with pirated software downloads or illegal or malicious websites. Watch the source of the download.
- If you become a victim of cybercrime, particularly financial crime, call the national (India) cybercrime helpline 1930 or file a complaint at https://cybercrime.gov.in/
- Configure Browse Safe DNS Servers on your devices to block phishing, malware, cryptojacking and other cyber threats
- If you are an enterprise, protect your organisation in real-time from cyber threats such as phishing, malware, newly registered domain names and other malicious communication using Shreshta Protective DNS. Please email info@shreshtait.com for a free 30-day trial.
Conclusion
In the last year alone, our threat intelligence team has seen a massive rise in threats impersonating Government agencies in India.
By impersonating various Government of India agencies as anchors, threat actors are leveraging social engineering techniques to make users comply with payment or installing software ridden with malware.
Free 30-day trial of our threat intelligence
Threat actors constantly optimise and evolve their attacks to steal credentials and data and infiltrate networks. Our threat intelligence feeds are highly actionable and curated to protect against phishing, malware, C2 and newly registered domain names.
Interested? Please send us an email to info@shreshtait.com for a free 30-day trial.
Similar threat intelligence posts you might be interested in,
